

Stay connected to the latest insights and news.

Mass Virtual and RAVE Computer Support USAF and Air National Guard
RAVE Computer and Mass Virtual have formed a powerhouse collaboration that tests, iterates, and fine-tunes their solutions to deliver the best possible combined performance. This joint effort ensures that end users have access to cutting-edge tools that not only enhance efficiency but also elevate team readiness to the next level.

RAVE Showcases Large Selection of Compute at IITSEC 2024
RAVE Computer, a leading manufacturer of solution-focused customized computer hardware and systems, will showcase a variety of form factors and system configurations from small form factors (SFF) to short-depth rackmounts, highlighting its commitment to delivering tailored solutions for unique project requirements.

RAVE Computer at IITSEC 2024
RAVE Computer will showcase its biggest-ever selection of optimized compute at I/ITSEC 2024 in Orlando, FL this Dec 2-5. Featured systems include the RenderBEAST series of GPU-optimized compute, as well as short-depth rackmounts and small form factor systems.
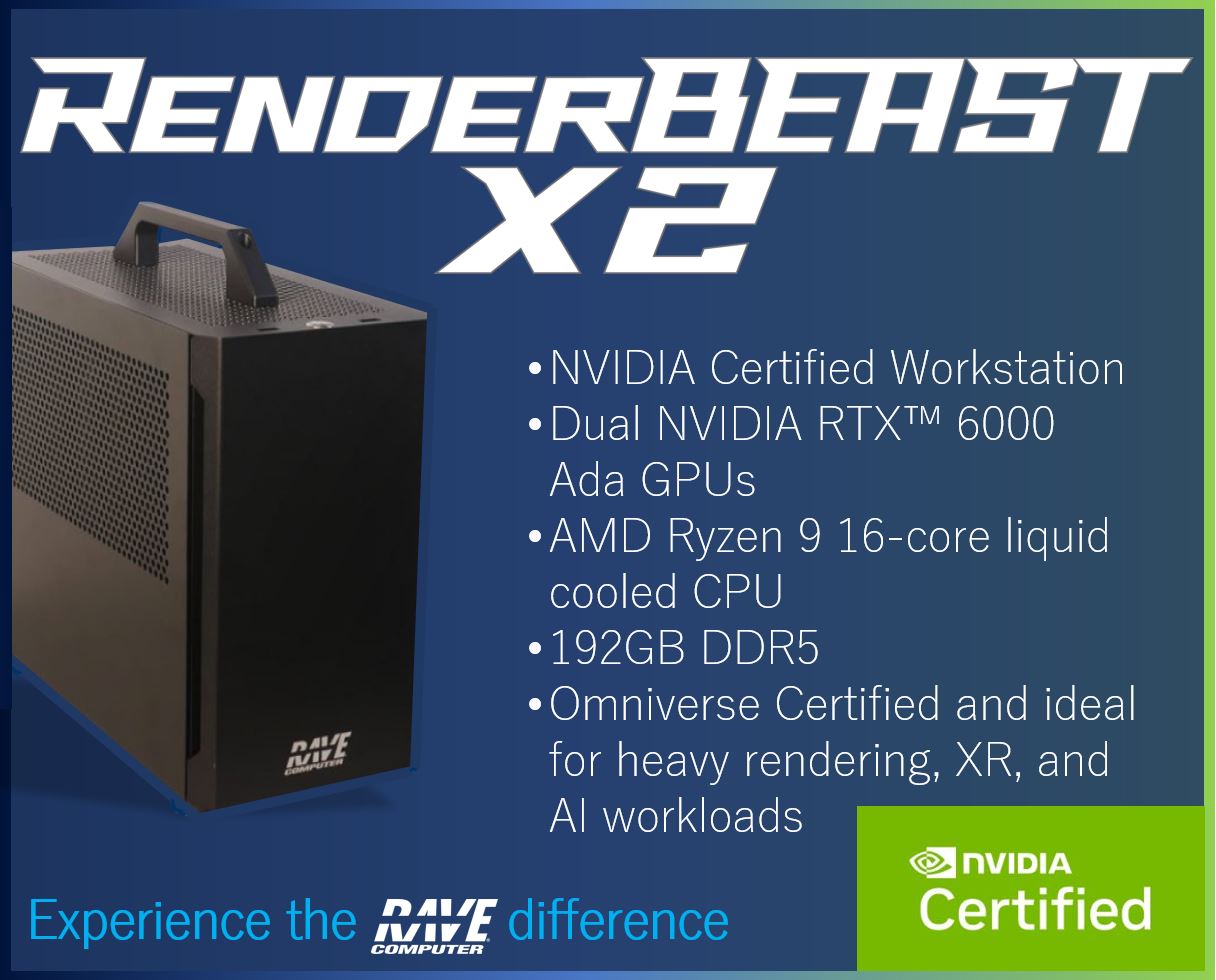
NVIDIA Certified Dual Ada GPU Workstation
RAVE’s RenderBEAST X2 workstation with dual NVIDIA RTX™ 6000 Ada Generation GPUs is NVIDIA Certified, Omniverse Certified, and Varjo Certified for the most demanding workloads. Whether your use case requires intense rendering for photogrammetry and geospatial programs, AI and LLMs, digital twins, or automotive and architectural loads, the RenderBEAST X2 provides the power and stability needed to get the job done.
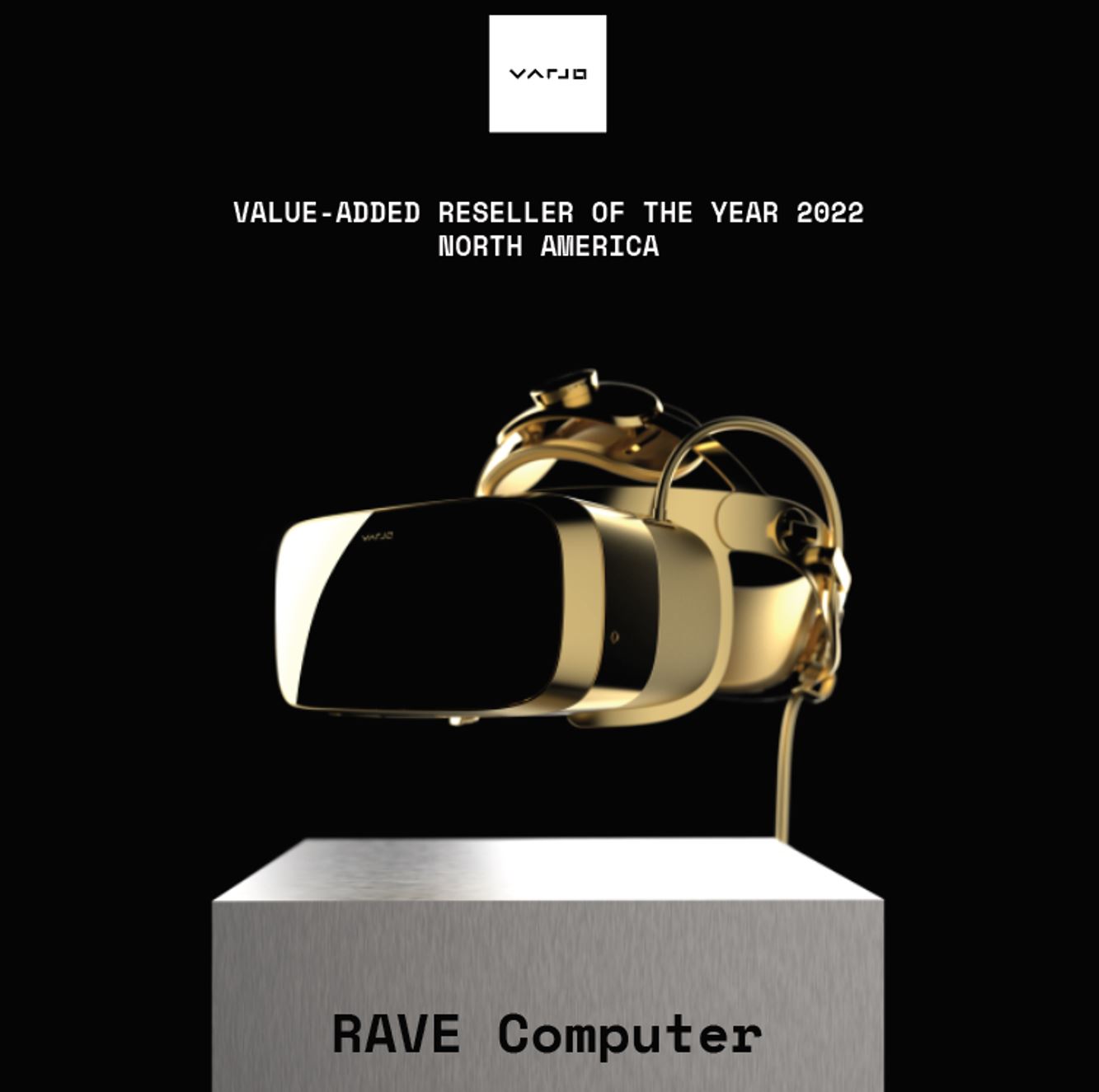
RAVE Computer Honored as Varjo ‘Reseller of the Year’ Third Year in a Row
“RAVE is honored and thrilled to be named Varjo’s Reseller of the Year for North America once again,” said Stacey Ferguson, President of RAVE Computer. “This remarkable achievement underscores not only our steadfast partnership with Varjo but also the pivotal role of our RenderBEAST computers in amplifying the brilliance of Varjo’s products.”

RAVE Introduces RenderBEAST X2 at GTC 2024
RAVE debuted the new RenderBEAST X2 workstation featuring dual Ada GPUs for maximum performance. The RenderBEAST X2 is NVIDIA Certified and optimized for Omniverse workloads. RAVE Systems Engineer Matt Moy presented “Real Time Ray-Tracing in XR: Do You Have What It Takes”, which dug into the careful balance of hardware, software, and dataset priorities to consider when building a realistic immersive XR experience.
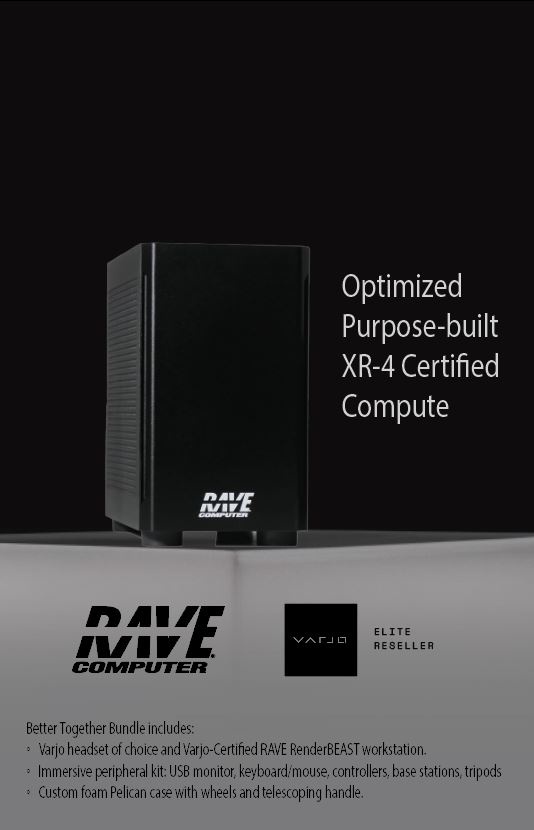
MultiGPU RenderBEAST XLT powers new Varjo XR-4 headset at I/ITSEC 2023
RAVE Computer showcased the new Varjo XR-4 headset in a stunning new demo at I/ITSEC 2024. The collaborative Omniverse-based sand table demo featured Varjo’s new XR-4 headset powered by the new RenderBEAST XLT – a multi-GPU tower leveraging multiple Ada GPUs. “RAVE’s collaboration with Varjo and NVIDIA reflects our dedication to advanced training and simulation in the defense industry,” shared Stacey Ferguson.
RAVE Computer at IITSEC 2023
RAVE Computer will showcase multiple innovative product upgrades and launches at I/ITSEC 2023 Booth #1059 – including TAA compliant multiGPU tower/rackmount solutions, RenderBEAST workstation and laptop, and new Backpack PC expected to launch in 2024. Live demos feature content from NVIDIA, Cesium, Bohemia, and ESI.

Five Reasons You Need A RenderBEAST Workstation
Whether you need a device that can handle graphically intense architectural modeling or can power through military-grade training and simulations, the RenderBEAST™ has the power you need to get the job done. Our ruggedized, high-performance workstation outlasts the competition and is compact enough to take anywhere. Check out the top five reasons why the RenderBEAST is the solution you’ve been looking for.
Press Inquiries
RAVE Computer has specialized in computer integration for over 30 years and collaborates with customers to deliver purpose-built computing solutions for some of the most complex environments in the world. Contact us with press inquiries at 1-800-966-7283 or info@rave.com.
